Writing a programming book is a task that almost always proves to be much more difficult than expected, especially when dealing with mutable and unpredictable frameworks such as ASP.NET Core and Angular. Once again we had to wait for the release of the latest "final" version of Angular, just as already happened in 2017 with my previous book: Angular 5.0.0 version, initially scheduled for September 18th, was postponed for over a month ( October 23th) and then released on November 2 after no less than nine release candidates.
After that experience we all thought we couldn't experience anything worse, but we were wrong: the latest major release of Angular experienced a delay of over two months (from December to February) and was further delayed by fourteen release candidates, thus arguably being a world record of some sort.
Luckily enough, the wait is finally over: on the night between 6th and 7th February 2020, just over 24 hours ago, Angular version 9.0.0 was released on GitHub, thus allowing me to finish the book in due time and the publisher - Packt Publishing - to honor the expected release date, which had been set to February 11th.
Now that the expected schedule has been successfully met, I would like to spend a couple words - well, maybe a bit more than that - to tell you about a rather odd experience I had this afternoon while surfing the web. Truth to be told, there's a high chance that you've heard similar stories already: however, I personally think that such kind of fun facts never gets old enough; other than being hilarious, they can also greatly help to understand how the web that we're browsing nowadays actually works.
So, while issuing some search queries on Google to calculate the SERP indexing level reached by the sites that had the book available for preorder, I came across this strange twitter post:
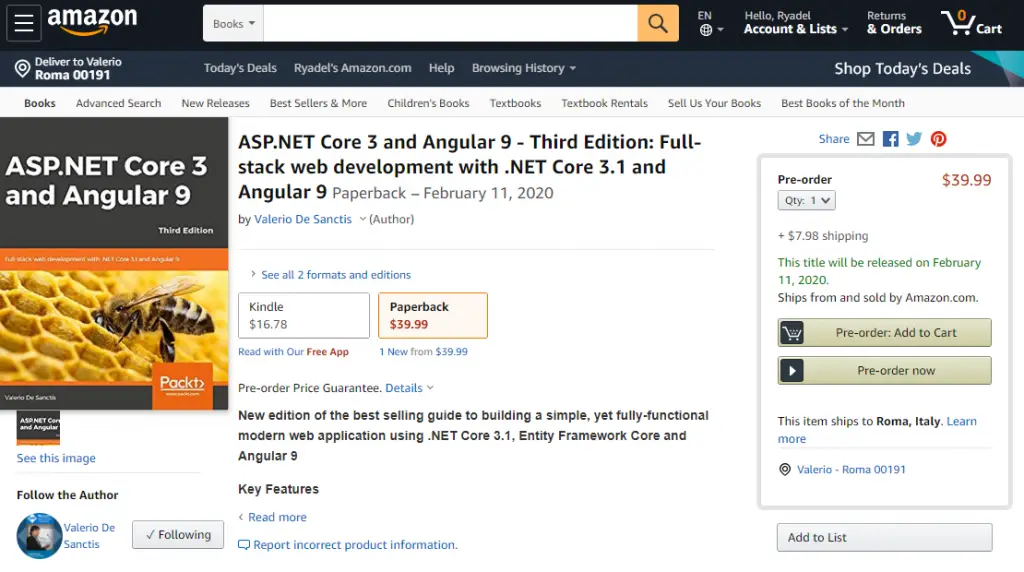
There was no mistake there: the post was clearly mentioning my book, with matching ISIN, name, author and description; and it was also telling me to download it for free (in e-book format) my clicking on an unidentified link. Such truly incredible opportunity could be seized since February 4th, judging by the tweet's time stamp: 7 days before the book's planned release date, and - most importantly - 2 days before I've actually finished writing it (!)
The twitter profile was just like you might expect from a fake account: owned by Christine H. McAndrews, a cute girl with zero followers, registered in January 2020, and only tweeting about forthcoming books and how to download them. Needless to say, each and every link was pointing to the same website.
Given such intriguing scenario, I couldn't avoid taking a look to the website itself!
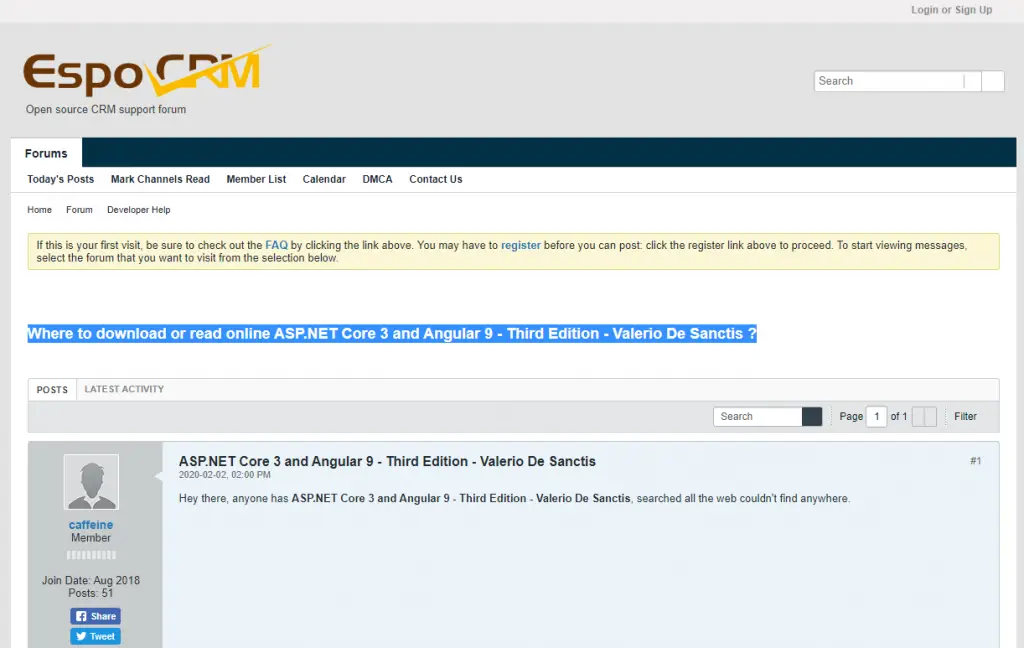
Eventually, I landed on a blatant scam page who looked just like a bulletin board system, where some (fake) users were enthusiastically talking about my book:
The page worked in a rather fun way that deserves a couple words: it was programmed to "dynamically" fill a series of placeholders with the book info (name, author, and so on) brought by the URL GET parameters: those placeholders were scattered within the page, thus trying to emulate a plausible "thread" of enthusiasts who were talking about the book.
Such neat mechanic allows "Christine", who's obviously an automatic tweet-bot, to spam the same URL in her posts, filling the GET parameters with the metadata taken from the upcoming books she wants to "promote"; a great bait for any unwary twitter (or google) user looking to download them at no cost.
(side note: the GET parameters also included the image URL for the book cover hosted on Amazon; unfortunately, the fake page doesn't seem to have properly implemented it, since it's not showing anywhere).
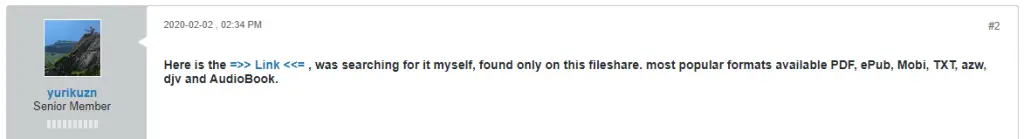
The fake thread developed by the page portrays a rather predictable scene, typical of online scams. The opening message is written by a user which is desperately looking for the book because he/she can't find it anywhere; a (fake) user responds to the request, suggesting a link to a "free e-book download" service (the actual scam website):
The scam attempt continues by staging the typical gimmick of the doubt dispelled by the denial, a trivial social engineering trick to win the trust of the potential victim and push her to perform a potentially risky call-to-action: the (fake) opening poster replies objecting that that site asks for a credit card ...
... but is immediately reassured by another (fake) user who confirms the authenticity and reliability of the service: "don't worry, it's all trusted: just put the card in and proceed with the download!"
The trust level is further raised by the original (fake) user , who confirms that everything went really well; the credit card was just a way to check it was a real user, just like a CAPTCHA: now everything makes sense!
The scene ends with another couple of users who confirm the authenticity of the site and praise the characteristics of the service: the scam is served.
In the unlikely case you want to take a look at the "scam forum thread" page, you can access it by copying the following URLand pasting it in your browser's address bar:
- https://toositego.ml/az.php?q=ASP.NET+Core+3+and+Angular+9+-+Third+Edition+-+Valerio+De+Sanctis&i=https://m.media-amazon.com/images/I/61kIIUNGgLL._AC_UY327_FMwebp_QL65_.jpg
Needless to say, you should only do that if you know what you're doing: although the page currently doesn't host malicious scripts, nothing prevents the administrators (aka the scammers) from change such behavior in the near future; however, the real threat is inside the suggested "download link" that appears within the thread: be sure to not visit it, let alone enter your credit card or any other data anywhere.
Conclusion
I must honestly say that this scam really surprised me: I was aware of similar tricks, but seeing my name (and book) inside that fake thread was rather awkward.
If you want to take a look at the ASP.NET Core 3 and Angular 9 book without scam pages, remember that you can do it for free by taking advantage of the PDF previews available on Amazon and on the publisher's websites at the following URLs:
- ASP.NET Core 3 and Angular 9 su Amazon.it
- ASP.NET Core 3 and Angular 9 su Amazon.com
- ASP.NET Core 3 and Angular 9 sul sito Packt Publishing
I hope you'll enjoy the book at least as much as this story!