Benefits of Cloud Application Development with AWS A list of good reasons to migrate your on-premise IT infrastructure to Amazon AWS: scalability, Security, AI integration, and more
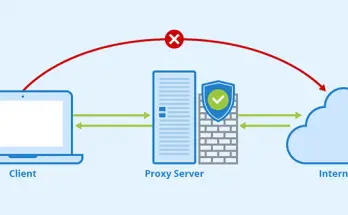
Cloud technologies are distributed digital computing technologies that make computing resources available to an Internet user as an online service. The advantage of this technology is that users can access …
Benefits of Cloud Application Development with AWS A list of good reasons to migrate your on-premise IT infrastructure to Amazon AWS: scalability, Security, AI integration, and more Read More