If you're a System Administrator and you had to perform a Risk Assessment, Security Assessment, Due Diligence or Compliance Questionnaire at least once, you most likely know that in order to meet the security requirements asked by most modern regulations and standards - such as the ISO/IEC 27001:2013, ISO/IEC 27002:2013, ISO/IEC 20000:2011, NIST CyberSecurity Framework, SSAE/SOC2, ITIL, PCI-DSS and so on - you have to setup your Windows Server environment accordingly. Since I've also been working on this, I'll share some basic knowledge that will be most likely useful for those who need to do that in a series of dedicated posts on this blog.
This is the first one of them, in which we'll be talking about setting up a Remote Desktop Session Time Limit for active, yet idle connections in Windows Server 2012.
Here's a common RA requirement that can be met in such way:
IT application and system sign-on mechanisms must be configured to limit the duration of any one sign-on session (session time-out). Session time-out is required for systems with payment card data if idle for more than 15 minutes.
That's something we can easily expect from a decent Risk Assessment questionnaire. Those who want to PASS this - assuming they're using Windows-based server machines - will need to adjust the behaviour of the Remote Desktop Session Host, which features no given timeout by default.
To do that, perform the following tasks:
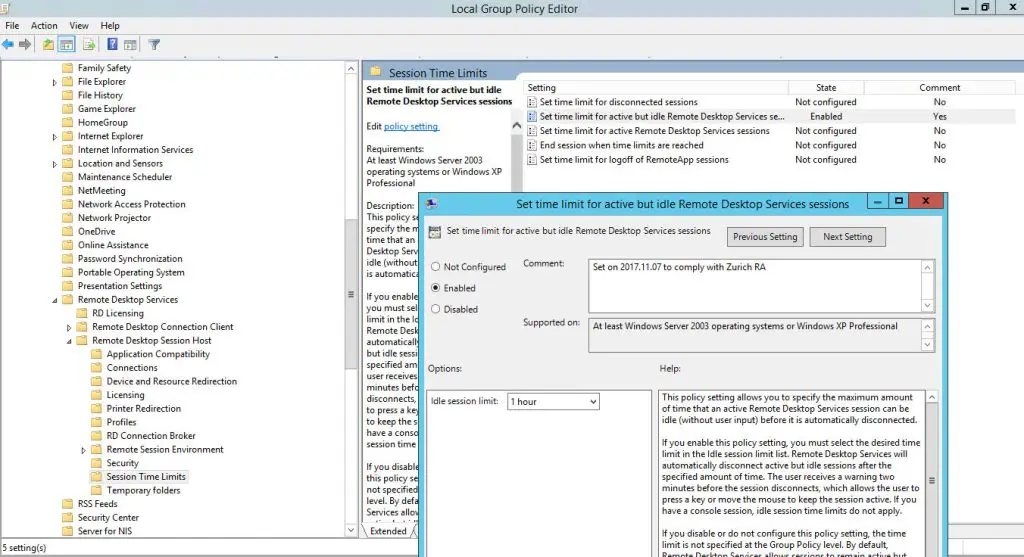
- Open a command-prompt and type gpedit.msc to launch the Local Group Policy Editor snap-in.
- In the left panel, expand the Computer Configuration node or the User Configuration node, depending if you want to change the RDS behaviour on system-scope (recommended for this scenario) or on users-scope (see below for the differences).
- Navigate to Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Session Time Limits.
- In the right panel, double-click the Set time limit for active but idle Remote Desktop Services sessions policy: in the modal window that will appear, activate it by switching the radio button from Not configured to Enabled, then set the desired amount of time in the drop-down list right below.
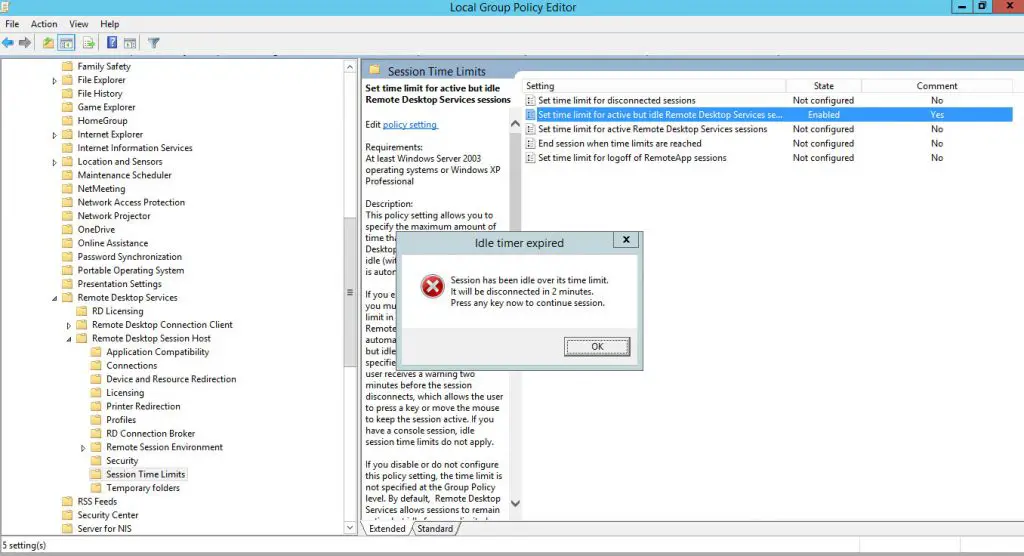
That's it! As soon as you click Apply, the new settings will be saved: from now on, all newly-initialized Remote Desktop session will be disconnected after the given amount of time. On top of that, the remote connected users will also have the chance to see the following alert popup, so that they will know what's about to happen and they'll have the chance to prevent the disconnection - in case they're still there:
Now our system is fully compliant with the above requirements.
Computer Configuration vs User Configuration
For those interested in dealing with the Microsoft-way of handling the global policy , it can be worth to briefly summarize the concept of Computer Configuration as opposed to User Configuration. In a given Group Policy context, Computer Configuration is applied to computers, regardless of who logs on to the computers; conversely, User Configuration is applied to users, regardless of which computer they log on to. If we set the settings collide with each other in Computer Configuration and User Configuration in one GPO, the Computer configuration will override the User Configuration. For details, please refer to the following article.



Don’t you need to use the “gpupdate -force” command?
AFAIK gpupdate is not working for this, at least in WinServ2k2012: you need to log out and back in.
source: https://social.technet.microsoft.com/Forums/ie/en-US/3a6f211d-d8d5-408a-8d37-b2fd8a4f09cb/2012-r2-rdp-admin-mode-set-session-time-limits-gpo?forum=winserverGP
Remote desktop is a rapidly growing technology today as it helps businesses to reduce costs, provide faster resolution to technical problems, convenience of providing support from anywhere etc. There are various remote support tools to select from such as R-HUB remote support servers, Logmein, GoSupportNow, GoToMyPC, Bomgar, etc. in order to remotely access computers.
Hi ,
I want to know when the pop-up window shows for RDP user?
Before the end of session time, there is 2 mins buffer time?
For example, I set the policy enabled with 15 mins, if it will show alert at 13rd min?
Thanks in advance
Michael
Yes, the warning pop-up window will show 2 minutes before the timeout.